Blockchain Technology and Cybersecurity: Enhancing Data Security
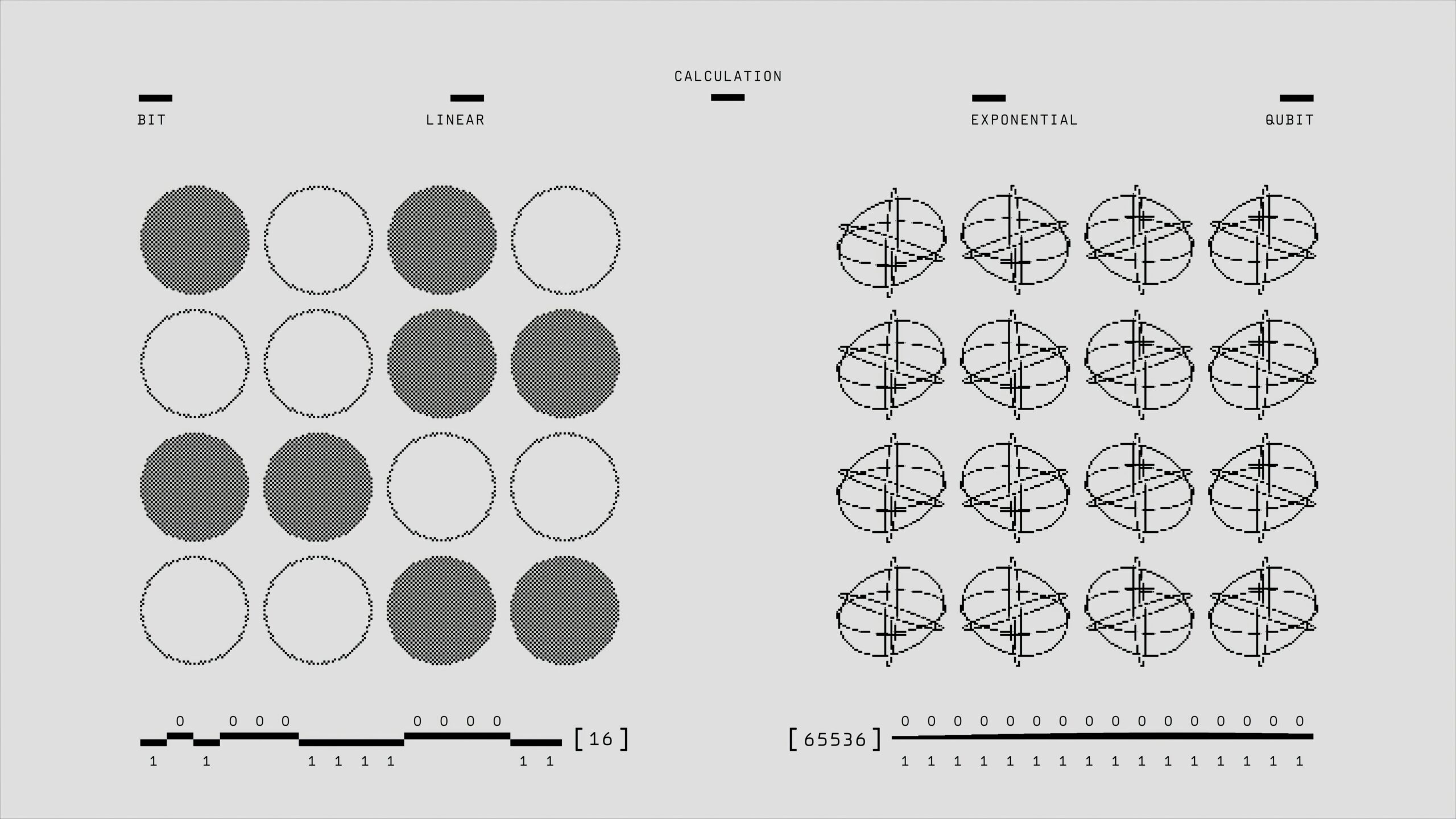
Introduction to Blockchain Technology Blockchain technology is a revolutionary system that is fundamentally changing the way data is stored, secured, and transmitted. At its core, blockchain functions as a decentralized ledger, allowing numerous participants to access and verify information in a secure manner. Unlike traditional centralized databases, where a single entity has control over the … Read moreBlockchain Technology and Cybersecurity: Enhancing Data Security